This repository contains the code for the Hardware Security course taught at KTH Royal Institue of Technology.
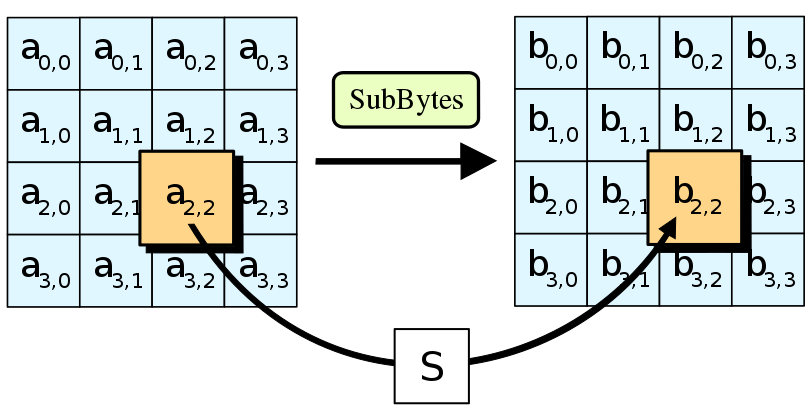
Side Channel Attack: Differential Power Analysis (DPA) on AES encryption algorithm to deduce secret keys
DPA can be performed as follows:
- Choose an intermediate value that depends on data and key vi, k = f(di, k)
- Measure power traces ti, j while encrypting data di
- Build a matrix of hypothetical intermediate values inside the cipher for all possible keys and traces vi, k
- Using a power model, compute the matrix of hypothetical power consumption for all keys and traces hi, k
- Statistically evaluate which key hypothesis best matches the measured power at each individual time