operating system: ubuntu18.04
compile:
Use Google's ASAN(https://github.com/google/sanitizers) for vulnerability detection. Specifically in Makefile, `add -fsanitize=address` to CFLAGS
make
test command: ./run_tests poc
{
"String" : {
"indexOf" : function (search) ,
"substring" : function (lo,hi) ,
"charAt" : function (pos) ,
"charCodeAt" : function (pos) ,
"fromCharCode" : function (char) ,
"split" : function (separator)
},
"Array" : {
"contains" : function (obj) ,
"remove" : function (obj) ,
"join" : function (separator)
},
"Object" : {
"dump" : function () ,
"clone" : function ()
},
"exec" : function (jsCode) ,
"eval" : function (jsCode) ,
"trace" : function () ,
"Math" : {
"rand" : function () ,
"randInt" : function (min,max) ,
"abs" : function (a) ,
"round" : function (a) ,
"min" : function (a,b) ,
"max" : function (a,b) ,
"range" : function (x,a,b) ,
"sign" : function (a) ,
"PI" : function () ,
"toDegrees" : function (a) ,
"toRadians" : function (a) ,
"sin" : function (a) ,
"asin" : function (a) ,
"cos" : function (a) ,
"acos" : function (a) ,
"tan" : function (a) ,
"atan" : function (a) ,
"sinh" : function (a) ,
"asinh" : function (a) ,
"cosh" : function (a) ,
"acosh" : function (a) ,
"tanh" : function (a) ,
"atanh" : function (a) ,
"E" : function () ,
"log" : function (a) ,
"log10" : function (a) ,
"exp" : function (a) ,
"pow" : function (a,b) ,
"sqr" : function (a) ,
"sqrt" : function (a)
},
"charToInt" : function (ch) ,
"Integer" : {
"parseInt" : function (str) ,
"valueOf" : function (str)
},
"JSON" : {
"stringify" : function (obj,replacer)
},
"result" : 0,
"configPATH" : undefined
}
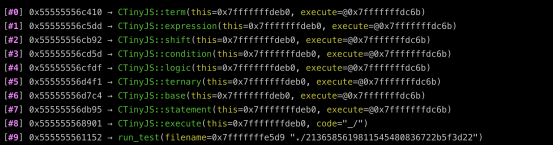
==20367==ERROR: AddressSanitizer: heap-use-after-free on address 0x60600000c538 at pc 0x000000441587 bp 0x7fff229a1790 sp 0x7fff229a1780
READ of size 1 at 0x60600000c538 thread T0
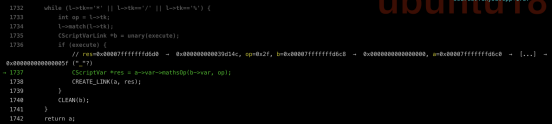
#0 0x441586 in CTinyJS::logic(bool&) /home/node/tiny-js/TinyJS.cpp:1853
#1 0x441dfa in CTinyJS::ternary(bool&) /home/node/tiny-js/TinyJS.cpp:1859
#2 0x442934 in CTinyJS::base(bool&) /home/node/tiny-js/TinyJS.cpp:1887
#3 0x442c52 in CTinyJS::base(bool&) /home/node/tiny-js/TinyJS.cpp:1902
#4 0x442634 in CTinyJS::ternary(bool&) /home/node/tiny-js/TinyJS.cpp:1876
#5 0x442934 in CTinyJS::base(bool&) /home/node/tiny-js/TinyJS.cpp:1887
#6 0x446011 in CTinyJS::statement(bool&) /home/node/tiny-js/TinyJS.cpp:1986
#7 0x44b23a in CTinyJS::execute(std::__cxx11::basic_string<char, std::char_traits, std::allocator > const&) /home/node/tiny-js/TinyJS.cpp:1322
#8 0x40718c in run_test(char const*) /home/node/tiny-js/run_tests.cpp:219
#9 0x4068b0 in main /home/node/tiny-js/run_tests.cpp:258
#10 0x7fa9198ef82f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2082f)
#11 0x406b68 in _start (/home/node/tiny-js/run_tests+0x406b68)
0x60600000c538 is located 56 bytes inside of 64-byte region [0x60600000c500,0x60600000c540)
freed by thread T0 here:
#0 0x7fa91a5d3b2a in operator delete(void*) (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x99b2a)
#1 0x44256e in CTinyJS::ternary(bool&) /home/node/tiny-js/TinyJS.cpp:1864
SUMMARY: AddressSanitizer: heap-use-after-free /home/node/tiny-js/TinyJS.cpp:1853 CTinyJS::logic(bool&)
Shadow bytes around the buggy address:
0x0c0c7fff9850: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c0c7fff9860: fa fa fa fa fd fd fd fd fd fd fd fd fa fa fa fa
0x0c0c7fff9870: fd fd fd fd fd fd fd fd fa fa fa fa 00 00 00 00
0x0c0c7fff9880: 00 00 00 05 fa fa fa fa fd fd fd fd fd fd fd fd
0x0c0c7fff9890: fa fa fa fa fd fd fd fd fd fd fd fd fa fa fa fa
=>0x0c0c7fff98a0: fd fd fd fd fd fd fd[fd]fa fa fa fa fd fd fd fd
0x0c0c7fff98b0: fd fd fd fd fa fa fa fa 00 00 00 00 00 00 00 00
0x0c0c7fff98c0: fa fa fa fa 00 00 00 00 00 00 00 00 fa fa fa fa
0x0c0c7fff98d0: fd fd fd fd fd fd fd fd fa fa fa fa fd fd fd fd
0x0c0c7fff98e0: fd fd fd fd fa fa fa fa fd fd fd fd fd fd fd fd
0x0c0c7fff98f0: fa fa fa fa 00 00 00 00 00 00 00 00 fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
==20367==ABORTING