FDM Monster is a server for managing your 3D printer farm through OctoPrint. Our efforts are focused on providing a professional print-farming workflow that is suitable for hobby and commercial farms alike.
This server has been battle-tested in the field for 100+ printers, so give it a star ⭐and enhance your 3D Printing Farm's workflow!
- Adding OctoPrint instances
- Dragging printers on grid
- Dropping GCode to print
- Batch select and print GCode
- Marking printers as maintenance mode
- Import printers from OctoFarm
- Raspberry Pi image MonsterPi
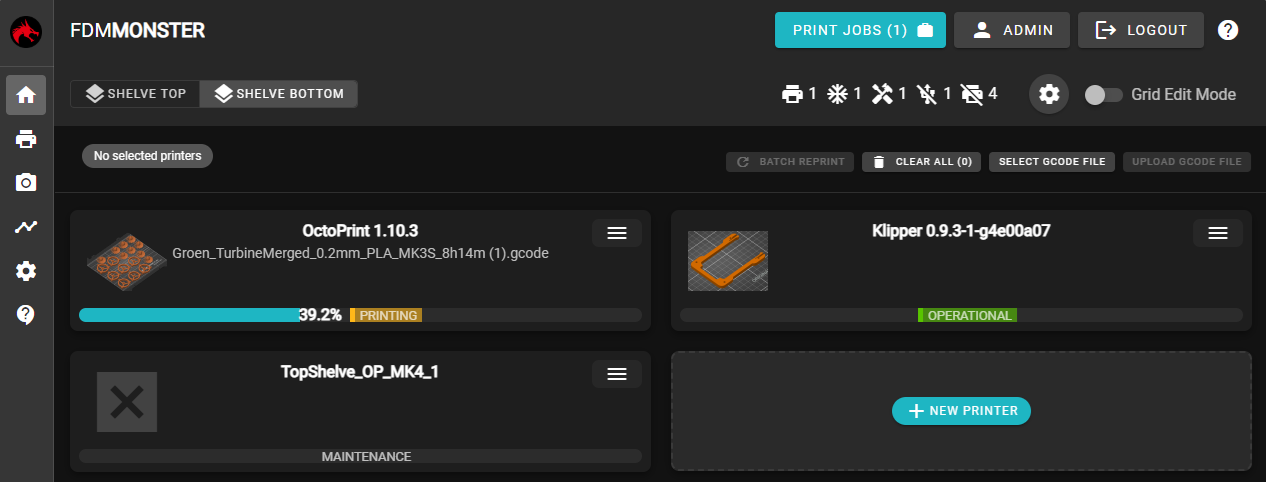 The FDM Monster grid after placing one OctoPrint instance.
The FDM Monster grid after placing one OctoPrint instance.
Check out the Documentation. Are you interested in running the Raspberry Pi image? Please jump ahead MonsterPi Section.
Please join the discord, but stay professional and proactive!
- Discord server: https://discord.gg/mwA8uP8CMc
- Website: https://fdm-monster.net
- Mail: [email protected]
These are the people involved in the project. Find the meaning of the emoji keys here.
Please consider sponsoring FDM Monster to help this project! You can find the GitHub Sponsorship Tiers here.
Thanks to the following parties for their financial support:
| Tier 4 | Tier 3 | Tier 2 | Tier 1 | One Time |
|---|---|---|---|---|
| WindArrow3d | doucettom | th3dstudio |
Feel like joining in as a developer or do you have a quick fix? Great! Please read the CONTRIBUTING file.
- 🚀 Docker amd64 image
- 🛡️ MongoDB 5 & 6 support
- 🚀 Quick copy paste of FDM Monster printers
- 🛡️ Complete API test coverage
- 🚀 Floor management
- Auto-clean old OctoPrint files (opt-in and configurable)
- 🚀 Windows and Linux Service
- Printer completion/failure tracking (with statistics page)
- Printer placement using drag n drop
- 🔌 Raspberry Pi image (https://github.com/fdm-monster/MonsterPi)
- 🚀 Documentation (https://docs.fdm-monster.net)
- 🛡️ Login and user management
- OctoFarm export
- Klipper and Moonraker API integration
- OctoKlipper integration
- Spoolman integration
FDM Monster is licensed with AGPL-3.0. For details, please consult the LICENSE file.
This project has been forked from OctoFarm at September 2021 when I ended as a contributor to this project.









