Comments (24)
Hi @stevespringett,
thanks for your quick and extensive reply. If the plugin is working as you're describing it could actually be an issue of SQ itself.
I checked my local SQ database and understood that each time the mvn sonar:sonar goal is executed (without any code change) all existing issue entries, their so-called "keys" and all SQ issue metadata (responsible person, status, etc.; as declared in SQ database) are staying the same. The issue, however, is that the contents generated by the plugin (affected dependency name, vulnerability description, etc.) is shuffled among the existing issue entries.
I hope I'll have some time to look into this issue in more detail. Once I have gathered more details I'll let you know.
from dependency-check-sonar-plugin.
Short update: This issue will only be fixed in Sonarqube 7.6+.
from dependency-check-sonar-plugin.
Hi,
please checkout new version of this plugin.
1.1.4 for Sonarqube 6.7.5 and above
1.2.3 for Sonarqube 7.6 and above
from dependency-check-sonar-plugin.
I have the same issue, its not the same setup but the result is the same. Issuse are mixed up resolved are changed to not resovled and the other way around.
Diffrence here is that Im using TFS and using SonarQube 6.7
from dependency-check-sonar-plugin.
@stevespringett as you seem to be the main maintainer for this project I would kindly ask you for your input to this issue. Is this a bug or a feature that is not yet implemented? If the latter is true I could try to work on some contribution in order to implement the feature.
from dependency-check-sonar-plugin.
Most SQ plugins add issues on the files they analyze. The Dependency-Check plugin does not do this, since in many cases, the dependencies are outside the source directory being scanned (i.e. .m2) or may not be present at all.
Therefore the Dependency-Check SQ plugin adds issues to the module level and does so using the SQ API as seen here.
This code is called by iterating through all the dependencies in the dependency-check-report and then for each dependency, iterating on all the vulnerabilities for that specific dependency. This results in issues being created in SQ on the module for each vulnerability in the DC report.
Comments, analysis decisions, table storage, etc are outside the scope of what this plugin is responsible for. That logic is internal to SQ. While I don't want to overreach and say that it's a SQ problem, there's a good possibility it is.
I'm prepping for a big launch in a few weeks on another opensource project I'm working on followed by a series of interviews and launch-related activities. I likely will not be able to dig into this until mid-April at the earliest. But if it does turn out to be an issue with this plugin, PR's are always welcome 😁
from dependency-check-sonar-plugin.
I am also witnessing the behaviour described by klemens-mang, using SonarQube 6.7.0 and version 1.1.0 of the dependency-check-sonar-plugin.
Looking at the SonarQube code for Version 6.7.3 (Tacker.java#L30), I think the problem might be the matching strategies (LineAndLineHashKey, LineHashAndMessageKey, ...), which are leaning heavily on the existence of a line number on an issue.
Your code does not seem to set such a line number (which line number should it choose, as you explain, you set the issue on the module). In that case, I think the first matching strategy, LineAndLineHashKey matches for each combination of issues, as Issue.line is always null and Object.equals() returns true if both elements are null. So, in essence, it's nondeterministic, which newly detected issue is matched against which already found one.
This theory seems to explain the described behaviour and I am currently experimenting with a work-around (assigning the issue not to the module, but to the input file of the dependency and choosing a line number based on the CVE number). But, I think, this approach is just a work around. Really, the matching strategies in sonar should be fixed, or, the API should make it clear, that line numbers are mandatory. What do you think?
from dependency-check-sonar-plugin.
you can see this idea in action in PR #61.
from dependency-check-sonar-plugin.
Reproduced with dependency-check-sonar-plugin 1.1.0 and SonarQube 7.1.
@stevespringett, kindly ask you to look into PR above.
from dependency-check-sonar-plugin.
@sschober I also think the underlying SonarQube matching strategy code likely needs changed. This is certainly a workaround (which appears to do the job - thanks @sschober), but I do think SQ needs to do some cleanup - or at a minimum remove the ability to create issues without a line number since that seems to mess everything up. This is likely an issue introduced between SQ4 and SQ7, as I do not remember older SQ versions having this issue.
from dependency-check-sonar-plugin.
Hello! Do you have solution for this problem? I have same mess in SQ 7.0 - my comments on issues in SQ are moving to other issues, and statuses are changed from opened to fixed. And some old issues became as new issues. I see it was solution in f5a1775 but it was revrted in 34f1c3a. Now I use sonar-dependency-check-plugin-1.1.3. and dependency-check-4.0.0 CLI. So, any help will be appretiated!
from dependency-check-sonar-plugin.
Hi @Kovshar-OS,
we try to link issues to project configuration file (pom.xml, gradle.build ...). Report files should not be uploaded to sonar.
At the moment it's a work in progress, see #99
If you have other projects then gradle or maven, i would appreciate, when you provide a very simple example project in our example folder.
You can also test the WIP merge request #99 and return feedback. Maybe it solves already your problem.
Best Regards
Reamer
from dependency-check-sonar-plugin.
Hi, Reamer! Thank you for response!
I'v compile sonar-dependency-check-plugin-1.2.2.jar plugin from sources in #99 and try to run it under SonarQube 7.0. For some reason( maybe version of SonarQube) it does't work (SonarQube falling dump when starting). So I returned to sonar-dependency-check-plugin-1.1.3.jar
Two words about my projects - both types - maven and gradle and I have a folder .git\lib with dependencies for projects.
But! I don't use maven or gradle scanner for project (I use sonar-scanner and depndency-check command line). So, can it be real to make issues from dependencies files(hash md5 etc)?
from dependency-check-sonar-plugin.
Hi @Kovshar-OS,
you are right the merge request #99 doesn't work with Sonarqube 7.0. I uploaded a new branch for Sonarqube 6.7 and above. This branch should work with your Sonarqube version.
I think it's no classic project setup with dependencies in .git/lib folder. In most cases your dependencies are downloaded with maven or gradle during build and then located somewhere else in your filesystem (definitely outside of git Repository). For example maven dependencies are located in ~/.m2/repository.
This plugin should be independently from sonar-scanner, gradle or maven. It using the generated reports from dependency-check (how ever they are created) and creates some issues and metrics in sonarqube.
At the moment Sonarqube has problem to identify issues which are linked to a maven module or a file without line number. See comment #55 (comment)
from dependency-check-sonar-plugin.
Hello Reamer! Thank you for response!
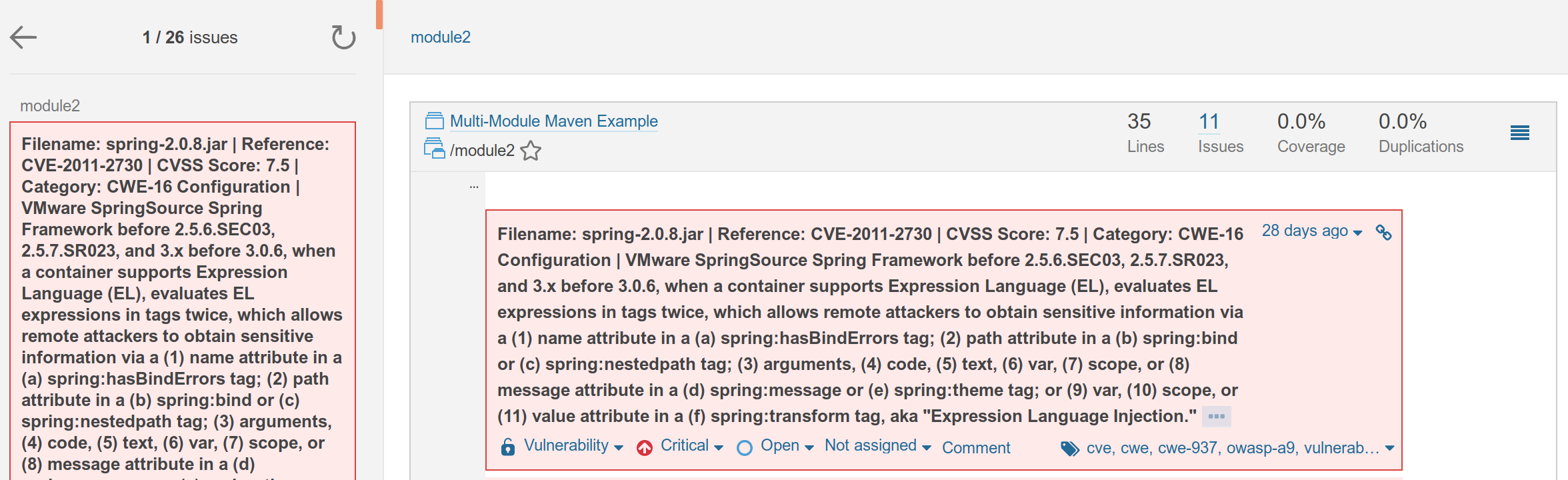
With new version of code, that you gave, I can succesfully run SonarQube. But situation with shifting key of issues in data base stay the same. Please look at the screenshot that I attached.

from dependency-check-sonar-plugin.
Hi @Kovshar-OS,
are the issues linked against module, file or file with line number?
from dependency-check-sonar-plugin.
Hi Reamer, can you explain how can I get this information.
(In database in Issues table column Line is null for created\changed dependency issues).
from dependency-check-sonar-plugin.
Hi, Reamer! Do you have some good news about fixing issue? Thank you!
from dependency-check-sonar-plugin.
Hi @Kovshar-OS,
thanks for testing the code. I had a few weeks off, sorry for late response.
You should see this information in your sonarqube dashboard.
Here some picture with all three cases:
Issue linked against file with line number

If I have enough time, I will fix the bug, so dependency issues are always linked to files with a line number. I'll let you know when the code is ready.
from dependency-check-sonar-plugin.
Hi, Reamer! Thank you for response! I will wait for fix. Thank you again!
from dependency-check-sonar-plugin.
Hopefully, that will get fixed soon as it is really crucial from CI/CD and security/release management perspectives.
from dependency-check-sonar-plugin.
Hi, Reamer! What about SonarQube 7.0 ?
from dependency-check-sonar-plugin.
Sonarqube 7.0 is a release, which is neither supported from sonarqube nor from this plugin. This plugin tries to support the latest LTS (6.7.x) and the newest version of sonarqube (at the moment 7.7). Because Sonarqube 7.6 has a major change in plugin API (see https://docs.sonarqube.org/display/DEV/API+Changes), i had to rewrite the whole plugin workflow.
If someone has sonarqube 7.6 running, they can test the current rewrite. (https://github.com/stevespringett/dependency-check-sonar-plugin/pull/99/files)
from dependency-check-sonar-plugin.
Should be fixed with actual version of this plugin. This plugin looks for a pom.xml or gradle.build in your project to link issue against this files.
from dependency-check-sonar-plugin.
Related Issues (20)
- Quality gate uses original severity of the issue, not the user assigned one HOT 7
- Can't see CVEs (vulnerabilities) on Sonar UI under Project>Issues. Used to see them in the past. Has anything changed? HOT 7
- False positive: NPM package ionicabizau/parse-url confused with parseurl HOT 2
- Examples and tests still use removed `sonar.dependencyCheck.reportPath` property HOT 5
- Cannot collspae Published Vulnerabilities in SonarQube HOT 6
- The dependency check scan is not uploading the reports when scanning a project HOT 3
- URI encoded package names do not match names in lock-file HOT 8
- Apache Log4j vulnerability HOT 3
- Support for Sonar 10.2 Software Quality Severities HOT 7
- [Quality Gates] : Owasp Dependency check HOT 1
- assets section of each release doesnt include .sha256 file HOT 1
- Integrate OWASP plugin with SonarQube from Azure Pipeline
- 9.0.2 of dependency-check plugin throws JSON parsing error with field "CvssV2.confidentialityImpact" HOT 4
- Update dependency-check-maven 9.0.X breaks Sonarqube Vulnerabilities report / JSON-Analysis aborted HOT 9
- NVD Api key config missing HOT 1
- SonarQube (Enterprise EditionVersion 10.3 --build 82913) Content Security Policy blocking the plugin resource HOT 7
- Html report break sonar UI
- Issue with Documentation for 10.2+ HOT 1
- Add "DownloadOnlyWhenRequired" to packaging HOT 2
- Update 5.0.0 Release Notes to Clarify SonarQube Version Compatibility HOT 2
Recommend Projects
-
 React
React
A declarative, efficient, and flexible JavaScript library for building user interfaces.
-
Vue.js
🖖 Vue.js is a progressive, incrementally-adoptable JavaScript framework for building UI on the web.
-
 Typescript
Typescript
TypeScript is a superset of JavaScript that compiles to clean JavaScript output.
-
TensorFlow
An Open Source Machine Learning Framework for Everyone
-
Django
The Web framework for perfectionists with deadlines.
-
Laravel
A PHP framework for web artisans
-
D3
Bring data to life with SVG, Canvas and HTML. 📊📈🎉
-
Recommend Topics
-
javascript
JavaScript (JS) is a lightweight interpreted programming language with first-class functions.
-
web
Some thing interesting about web. New door for the world.
-
server
A server is a program made to process requests and deliver data to clients.
-
Machine learning
Machine learning is a way of modeling and interpreting data that allows a piece of software to respond intelligently.
-
Visualization
Some thing interesting about visualization, use data art
-
Game
Some thing interesting about game, make everyone happy.
Recommend Org
-
Facebook
We are working to build community through open source technology. NB: members must have two-factor auth.
-
Microsoft
Open source projects and samples from Microsoft.
-
Google
Google ❤️ Open Source for everyone.
-
Alibaba
Alibaba Open Source for everyone
-
D3
Data-Driven Documents codes.
-
Tencent
China tencent open source team.


from dependency-check-sonar-plugin.